Inadequate data sanitization puts enterprises at risk of breaches and compliance failures - Help Net Security
Robust and lossless data privacy preservation: optimal key based data sanitization | Evolutionary Intelligence
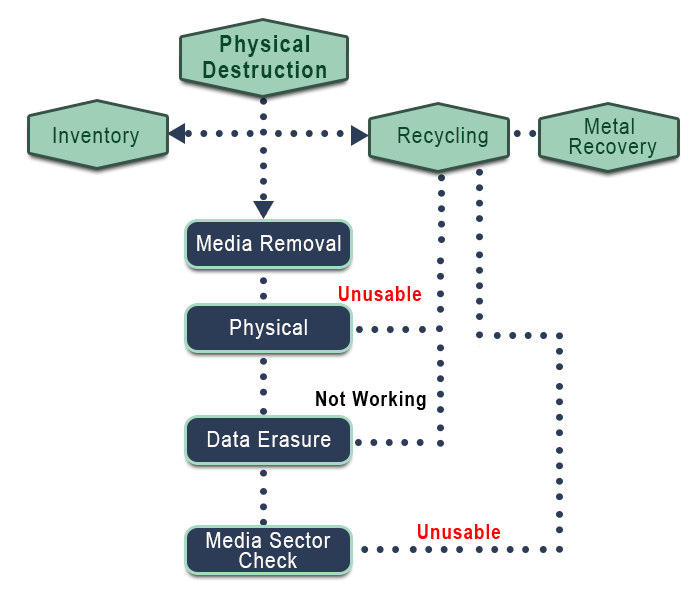
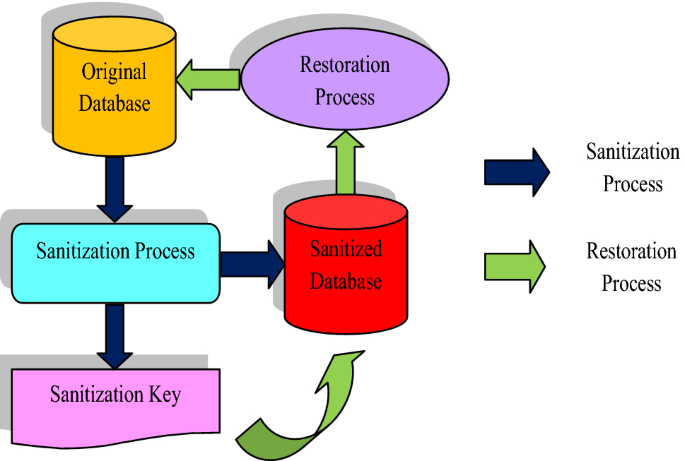
![PDF] Data Sanitization Framework for Computer Hard Disk Drive: A Case Study in Malaysia | Semantic Scholar PDF] Data Sanitization Framework for Computer Hard Disk Drive: A Case Study in Malaysia | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/a1a0c67f9045b9761a5094944585582adde92593/5-Figure2-1.png)
PDF] Data Sanitization Framework for Computer Hard Disk Drive: A Case Study in Malaysia | Semantic Scholar